Current Practice
Every internet user should have a basic understanding of passwords and security, unfortunately they don’t and this could lead to the compromise of their personal data.
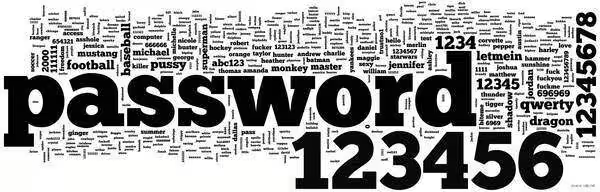
A security breach of an internet gaming site led to the publication of 32 million passwords on the internet. No personal information was given but the list of passwords proved very interesting. A study by Imperva showed the following:
30% of passwords where 6 characters or less
60% contained a limited set of alpha-numeric characters.
50% of passwords were names, slang words, dictionary words, consecutive digits, or adjacent keyboard keys.
The most common password among Rockyou.com account owners is “123456”, the 4th most popular “password”.
Password cracking is a 2 part process:
(1) Intelligent guessing– the first attempts will be based on most likely passwords so obvious ones like ‘password’ will be tried first (please don’t use password!). It will also use known passwords for the same username found elsewhere. But this will then move onto other dictionary words and names.
(2) Brute Force guessing – here a systematic guessing process will take place based on character combinations of increasing length. It is likely to start with lowercase and numbers as these are the most likely to be used.
The speed of modern computing and ADSL means that this process can become an increasing security issue.
Help is at Hand
Now it seems you are stuck between a simple password you can remember which is easily broken, or a meaningless jumble of characters that you forget. However that is not the case if you follow a 3 stage process of defence.
Stage One
Do not use a dictionary name word, or even a part of one and make sure you include at least one number, uppercase letter, lower case letter and another keyboard character (if you can). This will force an attacker past the intelligent guessing stage as your password will not appear in any dictionary or shortlist of possible passwords.
It will also make any brute force attack slower as the number of variables will go up.
Only numbers used – 10 permutations per password character.
Lower case letters and numbers – 36 permutations per password character.
Upper and lower case letters and numbers – 62 permutations per password character.
Upper and lower case letters, numbers and characters – 95 permutations per password character.
Stage Two
Try not to use the same username or password combinations for multiple web sites. Most definitely not for a social network site and your banking.
This will reduce the chance that a website you joined years ago is compromised (like the above example) and your personal information is matched to the username and passwords – a serious security risk to you.
If you want to use a standard password or username, try to adapt it slightly for each website – that way it is a little harder to guess. The adaptation could be as simple as using shared characters from the site name or some other variable you can remember.
Stage Three
Make the password as long as possible.
Groan! I knew you were going to say that, but that is the nub of the problem – that is why I use a short memorable password in the first place.
‘Password Padding‘ to the rescue!
Once a brute force guessing approach starts the most important factors are the variable characters which forces the use of more permutations, and password length. You’ve done the first bit in stage one, so an attacker has to go through all the simpler passwords first, then onto the more complex ones, as you’ve hidden Upper case letters (eg: AZ) and special characters (eg:()*!) in your password.
The second is length and that is where Password Padding comes into it.
An attacker does not know the length of the password. He might know the maximum length based on the rules of the web site and has no idea of the composition of your password, nor how close any guess might be as he gets no feedback with a wrong guess. He can try a list of the obvious ones first, but we know that will not work.
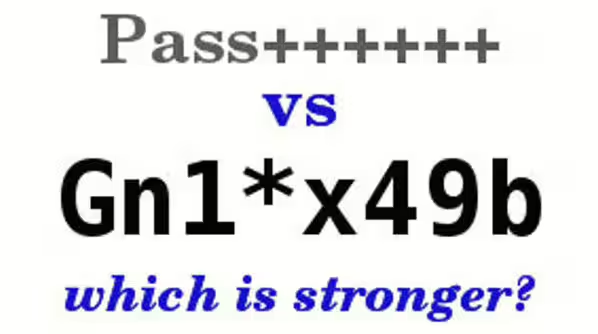
Consider the two passwords below :
T4u…….
Qy0$1xL5#
The first one is 10 characters long, uses a character set based on 95 permutations which gives 60,510,648,114,517,017,120 possible passwords, but importantly is very EASY to remember (T4u followed by 7 dots).
The second is only 9 characters, also uses a character set based on 95 permutations which gives only 636,954,190,679,126,495 possible passwords, but is very HARD to remember (it would also take 200,000 centuries for an online attack to crack, compared to over 19 million centuries for the easier to remember one!)
By contrast Qy0$ at 4 characters, but with 95 permutations gives only 82,317,120 possible passwords to be gone through (less than 23 hours online) and 123456 gives just 1,111,110 possibilities and could be broken in just 20 minutes in an online attack, assuming it is not the first one guessed!
So if you want to improve security make your password longer, and use the whole range of characters available to you.
Then keep it memorable by padding with multiple characters or use letters from a memory phrase or write it down and keep it safe – this might seem counter intuitive but you manage to keep your wallet or purse safe so put it here (most security experts would argue this is better than an easy to guess memorable password).
For a more technical discussion of the process check out Gibson Research Centre, with their ‘Haystack Calculator’ – a brilliant security site run by people with a better understanding of this than me.